Government cybersecurity agencies in both the United States and the United Kingdom have issued warnings regarding a sophisticated piece of malware known as Firestarter, which has demonstrated a remarkable ability to maintain its presence on Cisco network security devices even after firmware updates and security patches have been applied.
The malware has been linked to a threat group designated as UAT-4356 by Cisco Talos, an actor previously associated with cyberespionage operations including the ArcaneDoor campaign.
According to the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the U.K. National Cyber Security Centre (NCSC), attackers gained initial footholds on targeted systems by exploiting two specific vulnerabilities — a missing authorization flaw tracked as CVE-2025-20333 and a buffer overflow vulnerability identified as CVE-2025-20362 — affecting devices running Adaptive Security Appliance (ASA) or Firepower Threat Defense (FTD) software on Cisco Firepower and Secure Firewall platforms.
In one documented case involving a federal civilian executive branch agency, investigators observed a two-stage attack approach. The threat actor first deployed a malware component called Line Viper, a user-mode shellcode loader capable of establishing VPN sessions and harvesting sensitive configuration data such as administrative credentials, certificates, and private keys. Following this initial stage, Firestarter was then introduced to ensure long-term, persistent access regardless of subsequent remediation efforts.
CISA noted that while the precise exploitation date remains unconfirmed, the agency believes the compromise took place in early September 2025, predating the implementation of patches under Emergency Directive 25-03.
What sets Firestarter apart is its resilience. The backdoor is designed to survive device reboots, firmware upgrades, and security patches. If the malicious process is terminated, it relaunches automatically — a behavior made possible through deep integration with Lina, the core process underlying Cisco's ASA software.
A joint malware analysis report released by the two agencies details how Firestarter achieves this level of persistence. The malware hooks into signal handlers within the Lina process, which trigger reinstallation routines upon receiving process termination signals such as those associated with graceful reboots.
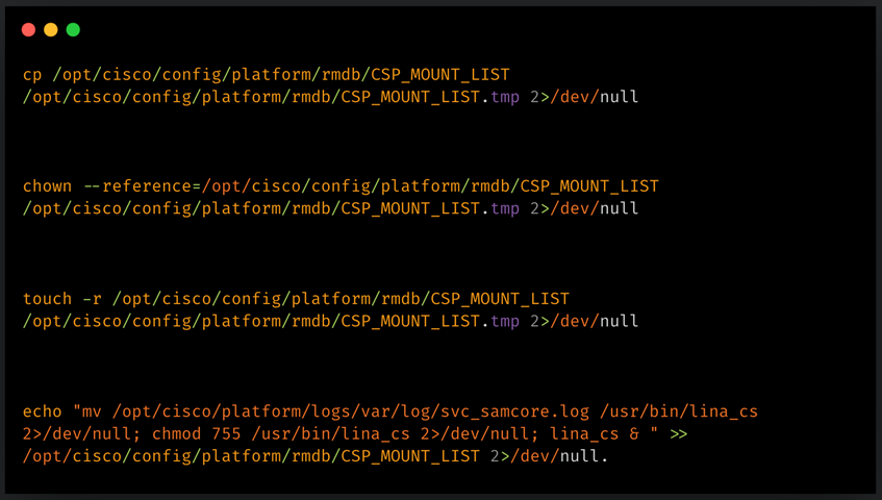
Additionally, Firestarter manipulates the csp_mount_list boot and mount configuration file to guarantee execution during system startup. The malware stores a backup copy of itself within a log file path at /opt/cisco/platform/logs/var/log/svc_samcore.log, and subsequently restores itself to /usr/bin/lina_cs, where it operates silently in the background.
Cisco Talos has independently published its own technical analysis of the backdoor, corroborating the persistence mechanism and providing further insight into the specific commands used by Firestarter to entrench itself within compromised systems.
The primary role of the Firestarter implant is to function as a backdoor, enabling remote access while executing shellcode provided by attackers.
To achieve this, Firestarter integrates with the Lina environment by altering an XML handler and injecting shellcode into the system's memory. This process creates a controlled execution path for malicious commands.
The execution of this shellcode is initiated through a carefully designed web VPN request. This request first verifies a hardcoded identifier before loading and executing the attacker's specified payloads directly in memory.
Though the Cybersecurity and Infrastructure Security Agency (CISA) has not disclosed specifics about the payloads that have been involved in attacks, Cisco has released a security advisory addressing the Firestarter threat.
This advisory outlines mitigation strategies and workarounds to eliminate the persistence mechanism associated with Firestarter, as well as indicators that can help identify the implant's presence.
Cisco is strongly advising users to reimage and upgrade their devices with the corrected software versions. This recommendation applies to both devices confirmed to be compromised and those that are not.
To assess whether a device has been compromised, administrators should execute the command ‘show kernel process | include lina_cs’. If any output is produced from this command, it indicates that the device has been compromised.
In situations where reimaging isn't an option, Cisco suggests performing a cold restart—powering off the device—to remove the malware. However, this method is discouraged due to the potential risk of database or disk corruption, which could result in booting issues.
Additionally, CISA has provided two YARA rules that can assist in detecting the Firestarter backdoor when applied to either a disk image or a core dump from an affected device.
A new wave of sophisticated exploits is on the horizon.
Attackers are now chaining multiple zero-day vulnerabilities,
bypassing critical security layers like renderer and OS-level sandboxes in a single attack.
To prepare,
join the upcoming Autonomous Validation Summit on May 12th and 14th.
Discover how advanced, context-rich autonomous validation
identifies exploitable weaknesses,
verifies that security controls remain effective,
and ensures the remediation process is fully completed.
Secure your place now to stay ahead of these emerging threats.
Why People Need VPN Services to Unblock Porn
Why People Need VPN Services to unblock porn is primarily rooted in the desire for privacy and unrestricted access. Porn unblocked refers to the ability to view adult content that is typically blocked due to geographical restrictions or censorship, a situation resolved through the use of VPN services. By masking a user’s IP address and securing their connection, VPNs provide a gateway to explore a wider array of online adult entertainment freely and safely.
Why Choose SafeShell VPN to Access Adult Content
If you want to access region-restricted adult content by unblocking porn sites, you may want to consider the SafeShell VPN. This service is specifically designed to help users bypass geographical limitations, providing a reliable gateway to otherwise inaccessible material while ensuring a private and secure connection.
The SafeShell VPN offers significant benefits for this purpose. It maintains high-speed connections essential for streaming without interruption, employs advanced encryption to keep your online activities completely anonymous, and features specialized modes that allow simultaneous access to content from multiple regions. Importantly, the SafeShell VPN can effectively unblock porn sites that are restricted in your area, all while supporting multiple devices so your protection is consistent across your phone, computer, and other platforms.
How to Use SafeShell VPN to Unlock Porn Sites
To begin using SafeShell VPN for accessing adult content from any desired region, the first step is to visit the official website and select a suitable subscription plan. After completing the purchase, download the SafeShell VPN application onto your device, whether it's a smartphone, tablet, or computer. Installation is typically straightforward and guided by on-screen prompts.
Once the app is installed, launch it and log in with your credentials. Navigate to the settings or connection menu to enable the specialized App Mode, which optimizes the VPN for application-specific access and enhanced flexibility. Then, proceed to the server selection screen within SafeShell VPN and choose a server location from the extensive global network that corresponds to the region whose content you wish to unlock.
After connecting to the selected server, open your preferred web browser or streaming application. You can now browse adult sites or platforms with the assurance that SafeShell VPN is encrypting your traffic and masking your real IP address. This ensures private, unrestricted access to geo-blocked content while maintaining your online anonymity throughout your viewing session.